Work-Bench’s post is one of the clearer attempts to name what’s happening: a new “agent runtime” layer built to execute, constrain, observe, and improve agent work at scale.
I mostly agree with that framing. Where I think it stops short is inside their “Constrain” pillar.
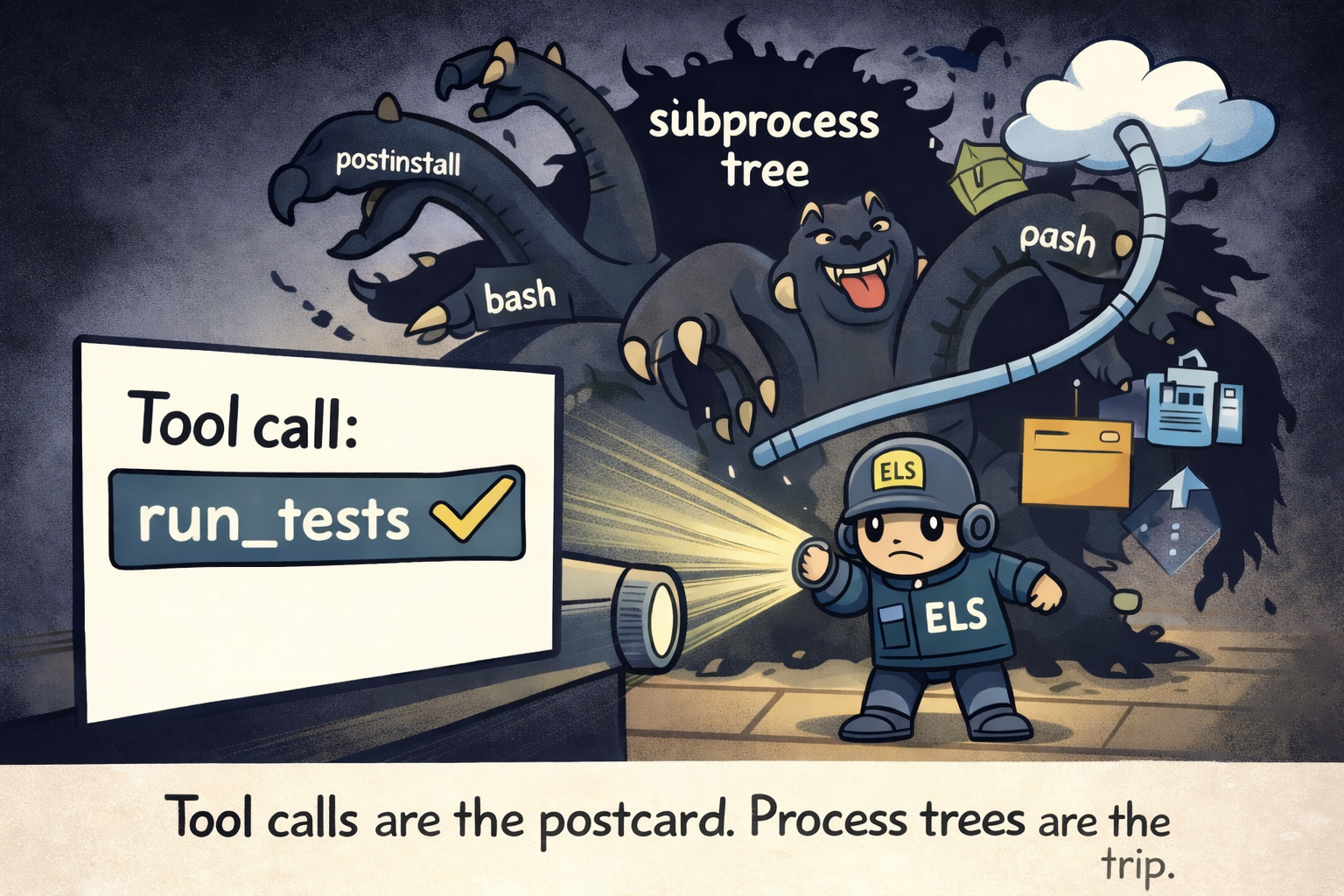
They explicitly define “Constrain” as “two things: identity and permissions.” That’s correct - but incomplete once you accept the premise of agents: they execute arbitrary code, spawn subprocess trees, and interact with the OS in ways that don’t map cleanly to “API permission checks.”
[Read More]